Our specialized assessment service provides a 360-degree security evaluation to ensure the resilience of your physical terminals, operating systems, applications, and network connections. We align our testing with global financial security mandates to protect sensitive customer data and prevent financial fraud.
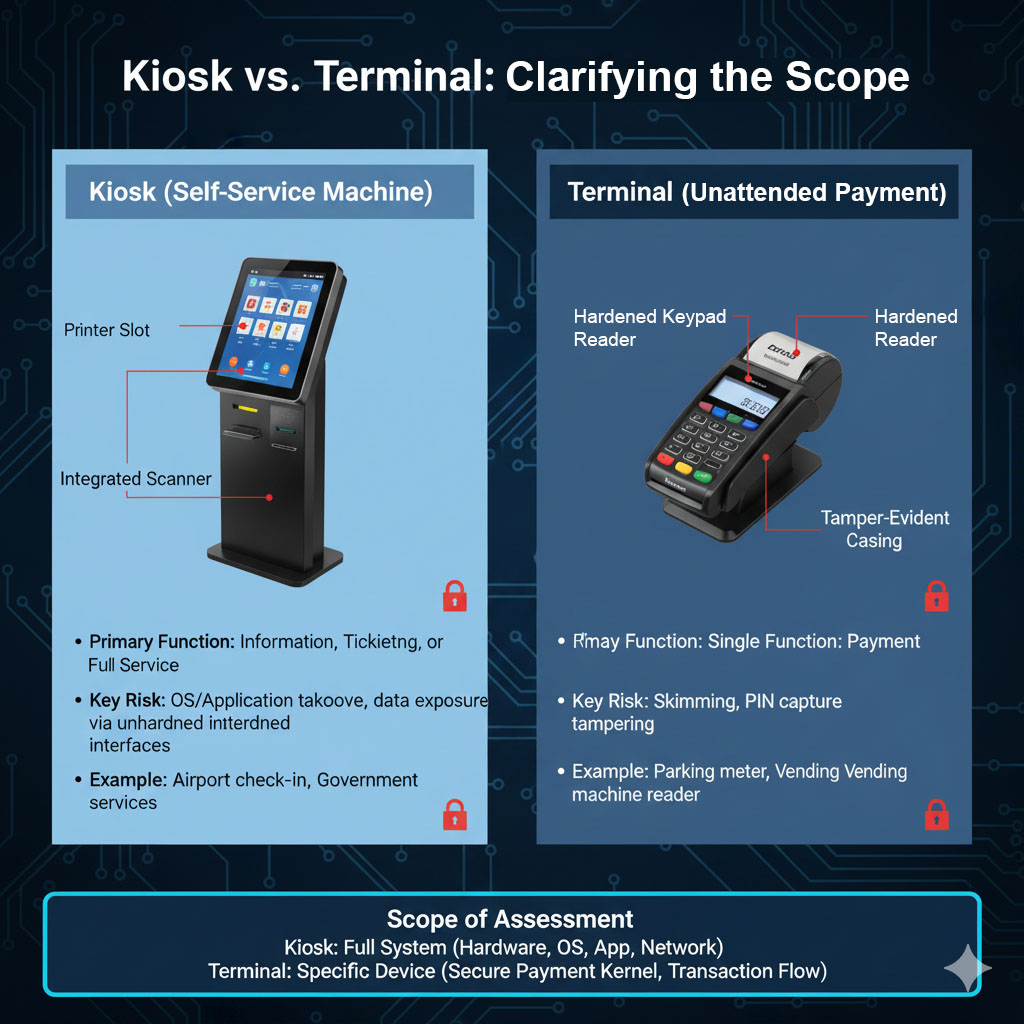
Kiosk vs. Terminal: Clarifying the Scope
Understanding the distinction between kiosks and terminals is crucial for a targeted security assessment. This illustration highlights their primary differences:
Methodology: How We Perform the Kiosk and Terminal Security Assessment
Our comprehensive assessment follows a structured framework, drawing heavily from PCI-PTS (PIN Transaction Security) guidelines, PCI DSS, and NIST SP 800-115 to address all vectors of attack on unattended environments.
| Assessment Layer | Key Objectives & Industry Standards |
|---|---|
| Physical Security Assessment | Objective: Evaluate resistance to hardware manipulation and unauthorized access. Method: Simulating physical intrusion techniques (e.g., lock picking, cover removal). Testing for effective tamper-evident seals and sensors. Checking for vulnerabilities to card skimming and keypad overlay devices, essential under PCI-PTS guidelines. |
| Operating System Hardening | Objective: Assess the security posture of the underlying OS. Method: Identifying and exploiting security misconfigurations (NIST SP 800-115). Verifying strict implementation of the Principle of Least Privilege (PoLP). Ensuring a complete system lockdown (kiosk mode) to restrict user access to the OS, file system, and unauthorized applications. |
| Application & Software Testing | Objective: Penetration testing of the user-facing application. Method: Searching for weaknesses related to the OWASP Top 10 for Desktop Applications (e.g., Injections, Broken Authentication). Testing for hardcoded credentials, insecure data storage, and the ability to inject or hijack DLLs or unauthorized code. |
| Network & Communications | Objective: Verify the security of data in transit and terminal connectivity. Method: Ensuring all data (especially PINs and card data) is encrypted end-to-end (Point-to-Point Encryption). Testing network segmentation and firewall rules to isolate the terminal from the corporate network. Assessing the security of remote access and management tools used for updates and monitoring. |
| Data & Key Management | Objective: Validate the protection of cryptographic keys and sensitive data. Method: Reviewing key management processes, including the security of the Key Injection Facility (KIF). Ensuring that cardholder data is never stored locally on the terminal’s disk (PCI DSS Requirement 3). |
Our Other Services
Our featured services divided into six (8) pillars as shown below. Whether you want to create, improve, assess, vigilant, resilient or receive professional trainings – we have you covered. Take a look below and click through the icons to learn more.
Don’t fall victim to Cybercrime
Speak to one of our consultants today!








