eKYC Breakthrough Test
The security of your digital onboarding process is paramount. Our eKYC Breakthrough Test service is a specialized, adversarial assessment designed to rigorously challenge and break the identity proofing controls that safeguard your electronic Know Your Customer (eKYC) workflow.
eKYC Breakthrough Test
The security of your digital onboarding process is paramount. Our eKYC Breakthrough Test service is a specialized, adversarial assessment designed to rigorously challenge and break the identity proofing controls that safeguard your electronic Know Your Customer (eKYC) workflow.

We move beyond typical compliance checks to simulate advanced fraud techniques, specifically targeting the core components of modern identity verification: Biometric Liveness Detection, Document Authentication, and API Integrity. Our methodology ensures your eKYC platform adheres to global fraud prevention benchmarks, giving you the confidence that your system is resilient against sophisticated identity theft and regulatory non-compliance.
| Key Benefits | Alignment to Industry Standards |
|---|---|
| Prove Resilience | Full compliance review with FATF (Financial Action Task Force) guidelines. |
| Defeat Deepfakes | Dedicated testing for Presentation Attack Detection (PAD), aligned with ISO/IEC 30107-3. |
| Ensure Integrity | Verify data security (in transit/at rest) against PCI DSS and general GDPR/Data Privacy principles. |
| Mitigate Financial Crime | Assess the effectiveness of integrated Anti-Money Laundering (AML) and Sanctions screening checks. |
Visualizing the eKYC Breakthrough Process
Here’s an illustration of the critical areas our eKYC Breakthrough Test targets to ensure robust identity verification:
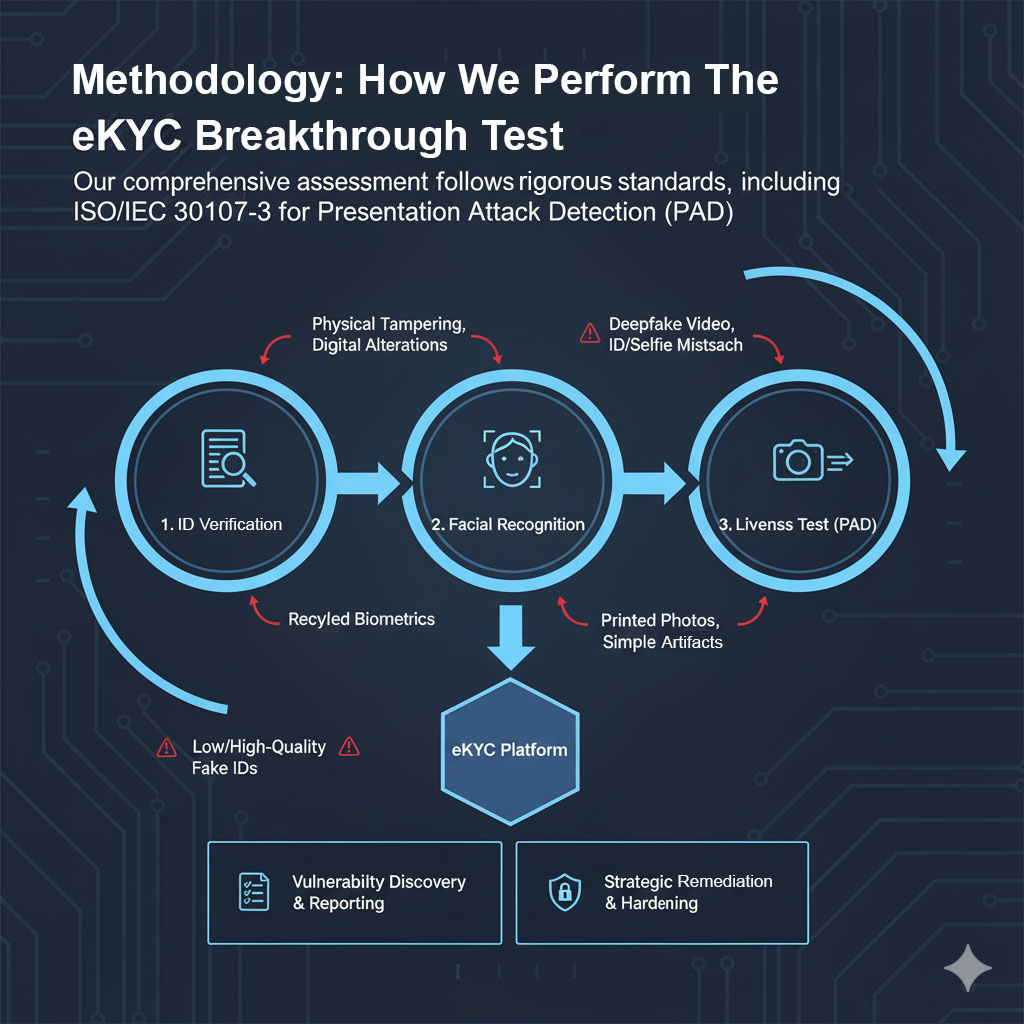
Methodology: How We Perform the eKYC Breakthrough Test
Our Breakthrough Test is an end-to-end, comprehensive assessment that strictly follows a process aligned with the requirements for mimicking malicious attacks on e-KYC solutions, including the rigorous standards of ISO/IEC 30107-3 for Presentation Attack Detection.
| Module | Test Scenarios (The “Breakthrough”) |
|---|---|
| ID Verification | Physical Tampering of ID (e.g., printed cards with alterations). Digital Tampering of ID (e.g., manipulated digital image files). Use of Fake ID (including low, medium, and high-quality fakes that may be produced by professional print shops). |
| Facial Recognition | Tampering of the selfie image without tampering the ID document image. Tampering of both the selfie and ID document image. Use of a different person’s selfie compared to the ID document. |
| Liveness Test (PAD) | Presentation Attack Detection testing in conformance to ISO/IEC 30107-3 standards, including: Use of simple artefacts (e.g., 2D masks, printed photos). Use of 3D masks and other sophisticated biometric artefacts. Use of falsified biometric traits created using Artificial Intelligence technology (DeepFake application coverage). |
Our Other Services
Our featured services divided into six (8) pillars as shown below. Whether you want to create, improve, assess, vigilant, resilient or receive professional trainings – we have you covered. Take a look below and click through the icons to learn more.
Don’t fall victim to Cybercrime
Speak to one of our consultants today!







